- 0 Posts
- 26 Comments
Unless someone has registered the trademark for those specific purposes you’re clear. A trademarks is only valid within a specific field of purpose. Trademarks are there to avoid consumers mistaking one brand for another.
There are a lot of entertaining articles on Techdirt about companies not understanding trademark law.

 9·4 months ago
9·4 months agoDoes anyone know of a list of TLDs that don’t allow reselling? I’d prefer to buy/lease one of those and let domain sharks play their own games.

 2·5 months ago
2·5 months agoI use gitit and it’s already packaged in most Linux distros.

 8·5 months ago
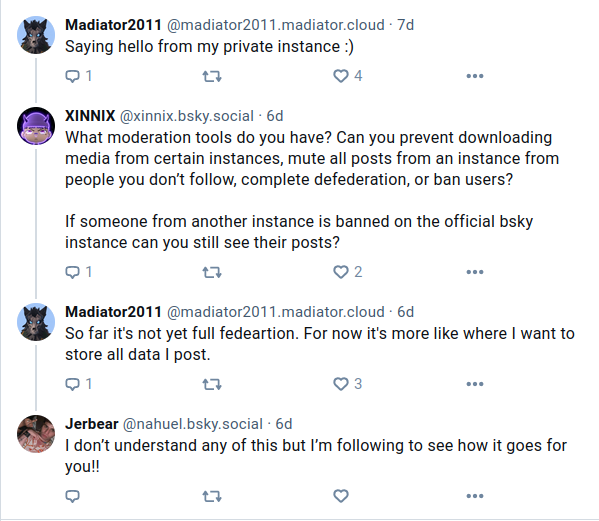
8·5 months agoTLDR; Sorta federation. It is possible to selfhost data.

 3·6 months ago
3·6 months agoYeah, that container probably crashed because of atmospheric disturbance.

 8·6 months ago
8·6 months agoI use Devuan and it’s just Debian without systemd.
Okay, but that would have made a shitty joke wouldn’t it?

Hmm… I don’t know maybe it’s fine as a joke.
Gothub is looking for a new maintainer.
Fontunately it’s just DNS.
Loop up the domains at one of: ns1.cloudns.net ns2.cloudns.net ns3.cloudns.net ns4.cloudns.net

 5·10 months ago
5·10 months agoAliasing and forwarding is not a good solution if you are concerned about law enforcement, because your personal e-mail is still linked with the tracker, just behind an extra hop and in addition you allow someone in between to read your e-mails. You had the answer yourself. Create a completely fresh free e-mail account somewhere, using as minimum a private tab to prevent tracking data to link anything to the account… and if you can get a free e-mail account with IMAP/POP access so that you can use it in an e-mail client to leak less data, do that.

 41·10 months ago
41·10 months agoIf you still want to respect user privacy, your analytics software could use the port of the connection instead of IP as the identifier. It would be perfectly fine for determining simultaneus users from the same IP, but not invasive enough to monitor an individuals behaviour. Don’t ask me which analytics software supports that. I’d grab the data from the http logs if it was me and use a tool like goaccess.

 2·11 months ago
2·11 months agoYou could check if a domain contains a lemmy instance by fetching
/.well-known/nodeinfo, but it’s bad netiquette to hammer sites with requests and could get users blocked. If you were to do it I’d make sure it cached the lookups in IndexedDB, localStorage or just using Cache API. I’m unsure how well any of the APIs works with UserScripts.

 20·11 months ago
20·11 months agoMarginalia Search perhabs.
Also these are worth mentioning:
- Mojeek have their own index. The results are occasionally a bit of a mess, but they are very open to input and have an account on Mastodon.
- Infotiger have their own index and the results are good.
- Alexandria which use the Common Crawl index.

 6·11 months ago
6·11 months agoI build a lot of tools like that and the first thing I do is to go to the developer tool in my browser and observe the network traffic. When you find the resource you’re after you scroll back and see what requests resulted in that URL. Going from those requests you figure out in the original static HTML document and resource, which parameters are used for the construction of the URL, that might require reversing some javascript, but that’s rare. After that you’ll have a pretty good idea how you obtain the video resource from the original URL. Beware of cookie set by the requests, they might be needed to access the next requests. For building my tools I use Perl or sometimes just Bash or a GreaseMonkey userscript to fetch and parse the urls and construct the desired output.
I use gitit from the Debian repositories. It’s a simple server application without a database and it uses git and pandoc. I just run
gitit -f somewiki.confand access it in the browser. As formatting you can use what pandoc supports, but I’ve chosen reStructuredText. DokuWiki mentioned by others in the thread is also a good option.

 1·1 year ago
1·1 year agoFrom reading the docs I get the impression that the client is discovering torrents from the DHT, and that’s also the data you can search from other clients. That means it wouldn’t be revealing anything about which torrents you’ve downloaded or are sharing.

 2·1 year ago
2·1 year agoWhy would you run linux.exe from Linux?


That’s the last stage of being a FOSS developer.